Zero-Tolerance Intrusion Prevention
Enterprise No Access Zones Detection & Autonomous Geofencing
Transform passive surveillance into active defense. Our AI agents monitor restricted perimeters and hazardous zones to ensure zero-harm compliance 24/7.
No Access ZonesDetection
The Challenges We Solve
High-Risk Blind Spots
Fatal accidents in mines or power rooms often occur in unmonitored “blind alleys” where help is far away.
Liability & Safety Hazards
Drowning or climbing accidents in schools/parks create massive legal liabilities and irreversible tragedies.
Slow Security Response
Traditional sensors can’t distinguish between a blowing leaf and a human intruder, leading to ignored alarms.
No Access ZonesDetection
Key Features of No Access Zones Detection
Our No Access Zones Detection evolves beyond simple motion monitoring through Smart Behavior Analysis. The system analyses the context, trajectory, and interaction patterns of any detected individual. It can distinguish between an authorised worker performing routine maintenance and an intruder attempting to bypass security protocols. This cognitive reasoning is powered by our AI Agent Development ecosystem, allowing the agent to evaluate multi-variant risk—such as how long a person remains in a restricted area or if they are moving with unusual intent. By integrating No Access Zones Detection with behavioural insights, we provide a proactive defense layer that adapts to complex human actions, ensuring uncompromised safety 24/7.
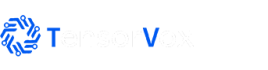
Real-Time Alerts
The cornerstone of our No Access Zones Detection is instantaneous human recognition. Traditional perimeter monitoring systems are plagued by false alarms caused by moving shadows, small animals, or environmental shifts. Our AI, calibrated for industrial precision, utilizes advanced computer vision to isolate the unique geometric and movement signatures of human silhouettes within milliseconds. This guarantees that No Access Zones Detection alerts are triggered only when an unauthorized person breaches a digital line, whether it is a physical perimeter or a sensitive indoor area. By ensuring 100% human-centric detection, we minimize operational downtime and allow security teams to focus on real threats, maintaining total facility integrity without unnecessary interference.
Multi-Item Detection
Integration of an active deterrent is a critical component of professional No Access Zones Detection. Our Audio-Visual Intercom module doesn’t just alert security; it initiates immediate, automated on-site communication. When a confirmed breach is detected, the No Access Zones Detection system can trigger a localized strobe light and issue a customized PA (Public Address) voice warning to the intruder. This immediate, localized action can often deter an intruder before they reach critical assets or hazardous areas. This two-way communication channel is a vital feature of our AIoT Integration, enabling remote security personnel to assess the situation visually and issue direct commands, effectively bridging the gap between detection and physical containment.
Instant Multi-Channel Alerts
The final, crucial layer of our No Access Zones Detection is Fail-Safe Integration. A standalone detection system is only as good as its weakest link. We leverage our extensive AIoT Integration expertise to ensure that once a critical breach is confirmed by the No Access Zones Detection logic, the physical response is absolute. The system can instantly send triggers to electronic lock gates, flash site-wide alerts, or even execute an emergency stop on nearby robotic arms or production lines. This fail-safe loop ensures that an intruder is physically prevented from moving deeper into a hazardous or high-value zone, making our No Access Zones Detection a true barrier to catastrophic incidents and maximizing workplace safety.

Smart Dashboard
No Access ZonesDetection
The AI Ecosystem Integration
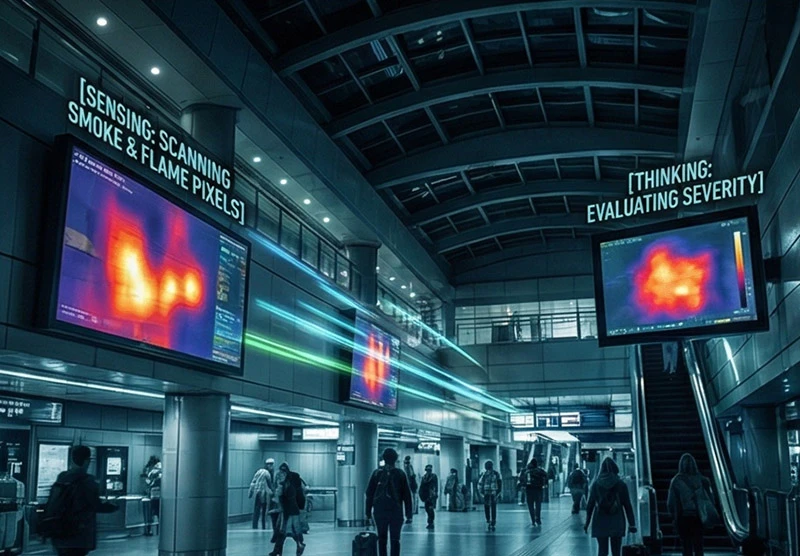
Sense (Video AI)
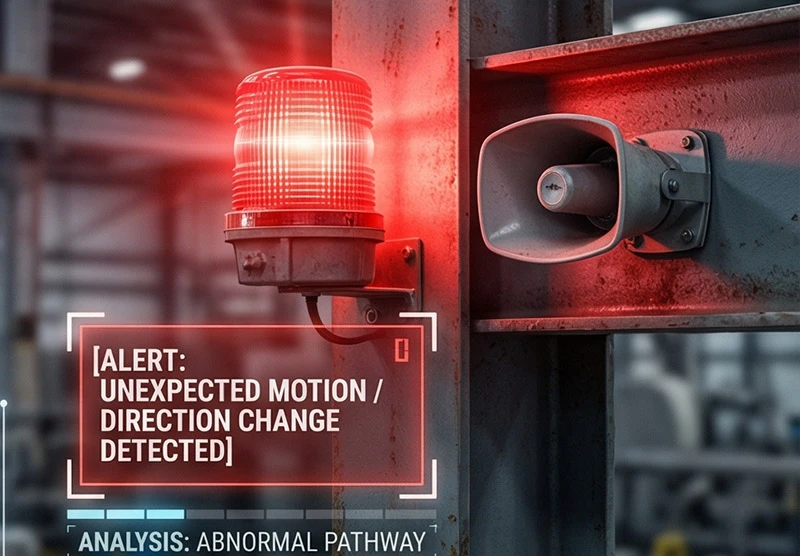
Our No Access Zones Detection begins with the creation of intelligent virtual perimeters. Using high-definition edge cameras, the system “Senses” the environment by mapping out specific coordinates that are off-limits to unauthorized personnel. Unlike physical barriers that can be bypassed, our AI vision monitors these zones with 100% spatial awareness. It ingests visual data in real-time, identifying the exact moment a human silhouette or a piece of unauthorized equipment breaks the digital line. This layer is calibrated to ignore non-human movements, such as shadows or small animals, ensuring that the sensing phase is both sensitive and highly accurate.
Think (AI Agent)
The “Think” phase is where our No Access Zones Detection differentiates itself through cognitive reasoning. Our AI agents don’t just detect movement; they evaluate Identity-Aware Analytics. The system checks if the person entering the zone has the correct authorization or is wearing the required specialized PPE for that specific area. By analyzing the trajectory and speed of the intruder, the agent determines the severity of the risk. This localized decision-making happens at the edge, allowing the system to process complex scenarios—such as distinguishing between a maintenance worker and a lost visitor—in under 100ms.
Act (AIoT)
The “Act” phase translates digital detection into a physical deterrent. Once a violation is confirmed by the No Access Zones Detection logic, the system triggers a multi-level response. This includes flashing strobe lights, activating localized PA voice warnings, and sending high-priority snapshots to the security dashboard. Through our AIoT Integration, the system can even execute an emergency stop on nearby machinery or lock electronic gates to prevent the intruder from reaching a high-danger point. This proactive intervention ensures that a breach is stopped before an accident occurs, maintaining total site integrity.
No Access ZonesDetection
Application Scenarios

Energy & Industrial Facilities
Monitoring coal mine goafs and power stations to prevent asphyxiation or explosions caused by unauthorized entry or risky behaviors like smoking.

Logistics & Infrastructure
Securing warehouses, reactor zones, and loading docks with smart geofencing to trigger automated alarms for critical facility protection.
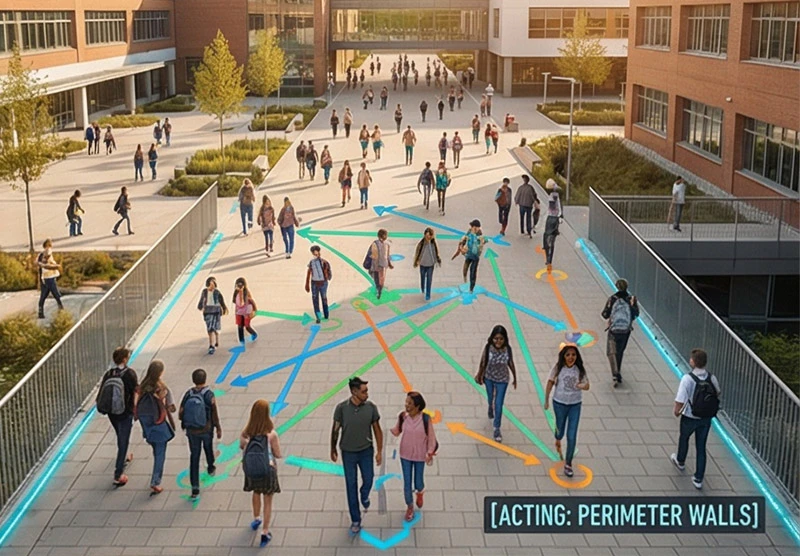
Schools & Public Spaces
Preventing student climbing or drowning incidents by monitoring school rooftops, perimeter walls, and artificial lakes in scenic parks.
High-Security Sensitive Zones
Integrated protection for prisons and military bases, linking AI vision with high-voltage pulse systems to prevent escape or unauthorized intrusion.

Transit & Tunnel Operations
Monitoring airport runways, subway tracks, and bridge maintenance zones to identify abnormal lingering or unauthorized access to track areas.

Specialized Healthcare & Hospitality
Managing fever clinics, isolation wards, and hotel rooftop platforms to safeguard restricted zones with human-detection analytics.
Our Value
Total Liability Protection and Asset Security.
Compliance & ROI
In Singapore, ensuring the safety of students, workers, and citizens is non-negotiable under WSH and NEA regulations. “No Access Zones” are your primary line of defense against catastrophic lawsuits.
By preventing just one major accident or security breach, the system pays for itself. Automation reduces the need for constant physical patrols, allowing your security team to focus on high-value tasks while AI guards the “dead zones.”
100% Audit-Ready
Reduce Fines
98% Accuracy
Ready to Optimize Your Space and Enhance Safety?
F.A.Q.
Find answers to commonly asked questions about our services and trading strategies
Our AI integrates with infrared (IR) or thermal cameras, allowing it to detect human silhouettes and movement even in 0-lux total darkness environments.
Yes. Our advanced AI Agent is trained to identify small objects and specific postures, flagging risks like smoking or phone use in flammable chemical zones.
We set virtual ‘danger lines.’ The system only triggers an alert if someone crosses the safety threshold toward the water or cliff edge, ignoring normal foot traffic.
Yes. Every intrusion is logged with a timestamp and visual evidence, making it easy to generate safety reports for MOM audits or internal compliance reviews.